Note: This post is the first in a series of breach review articles. No fear tactics. No click-bait. Just a rational discussion about the most recent breaches and how they might impact us from both an OSINT and privacy perspective.
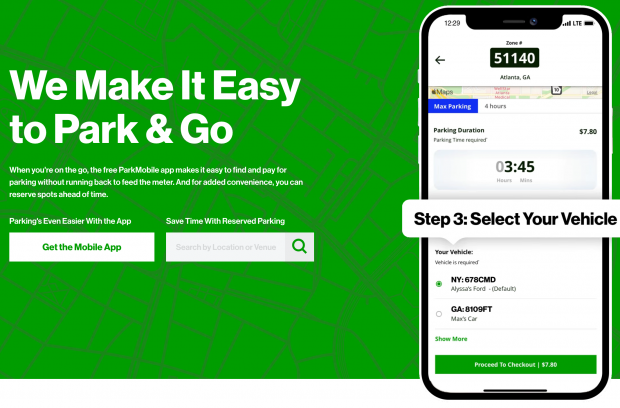
In early-April, various data breach communities began discussing a recent breach at ParkMobile, an app which makes parking payments more convenient. The company eventually released confirmation of the breach at https://support.parkmobile.io/hc/en-us/articles/360058639032. I obtained a copy of the data, which contains the following data structure.
CLIENT_ID,TITLE,INITIALS,FIRST_NAME,LAST_NAME,GENDER,DATE_OF_BIRTH,MOBILE_NUMBER,EMAIL,USER_NAME,PASSWORD,SECOND_PASSWORD,THIRD_PASSWORD,SOCIAL_SECURITY_NUMBER,ADDRESSLINE_1,ZIPCODE,CITY,VRN,DESCRIPTIONS
The data was presented within a single 5GB CSV spreadsheet with over 21 million entries. Attempts to create new accounts at ParkMobile with ten random email addresses within the breach confirmed that accounts already existed with that data. This provides anecdotal evidence that the data is truly from the company. The following is an actual record, redacted for privacy (XXXX), with explanations within parentheses.
1453797 (user number), 352256XXXX (telephone), 352256XXXX (telephone), [email protected] (email), [email protected] (email), $2a$05$mYZyhLkCMueaqAPWpxL7c.IJCEN9T3FILDLXGW0C/Dtu0QKvtAbXC,869JI,86XXXX (encrypted password), CGSXXXX (registration plate), CBSXXXX (additional plate), Dani,Escape,Escape,Cadillac,Escape,rental,Dani,Escape,Escape,Cadillac,Escape,rental (additional notes)
It appears that very few entries possess SSNs or DOBs. The raw data possessed telephone numbers for almost all entries, which were already stored in 10-digit format without hyphens or parentheses. This makes them easy to search. If my target was exposed in this breach, I could easily associate a name with email and cellular telephone number or vehicle and phone details with an email address. Overall, I find this breach to be very beneficial to online investigators. I plan to add it to my collection to query emails and telephone numbers during investigations.
From a privacy perspective, I believe this data is quite damaging to the typical customer. This breach reminds us that alias names, forwarding email accounts, and burner VOIP telephone numbers should always be used when providing personal details to any service. I suspect customers will soon begin receiving malicious email and SMS attacks.