I found myself in a nostalgic mood last week, longing for 90's Christmas gifts. I have always been a technology addict, and the annual Radio Shack catalog was my preferred option over the J.C. Penney's or Sears Holiday sections of their own ads. Somehow, I began thinking about how the mobile device has become a replacement for all of the amazing gadgets I had as a child and young adult. There were very few devices I could recall which were not available as a standard function within my mobile device. The following is my own trip down memory lane. I hope that you find something which reminds you of your own tech journey.
The Phone Itself: My first phone was a corded push-button tone-dial AT&T landline. It was a major upgrade from the household rotary-dialer. I spent countless hours calling my friends. Today, we rarely verbally talk to each other in lieu of text. Our mobile device makes voice calls easy with traditional and secure options. As a child, I could never have imagined the features we have today. I remember when Caller ID cost an extra $1 monthly and call-waiting was an upgrade.

The Cell Phone: My first cell phone was a Motorola early flip phone. It would soon be replaced by the Star-Tac and then a slim Nokia. The size was ridiculous and the battery life dismal. Today, a few hundred dollars buys us a slim device with touch-screen and two-day battery. However, I miss the audio quality of my first few devices.

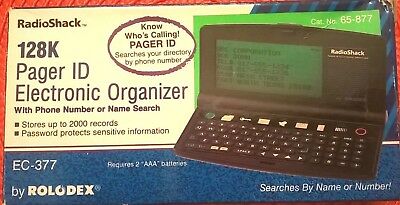
The Pager: I had a pager before I had a cell phone. My friends could call my number from their landline and enter their own number (or 80085) for a callback. I could be anywhere in town and be notified. It was an amazing time which we now take for granted. When the alpha-numeric options entered the scene, we were kings. Today, full text messages are available everywhere at no cost.

The Answering Machine: When I was young, voicemails only existed in the form of a voice message on poor-quality cassette tapes which could be heard by the entire family. Today, we have voicemail through unanswered cell calls, but receiving one is rare. Instead, all major communications apps have the ability to upload an audio recording for immediate delivery. We no longer wait for the beep.

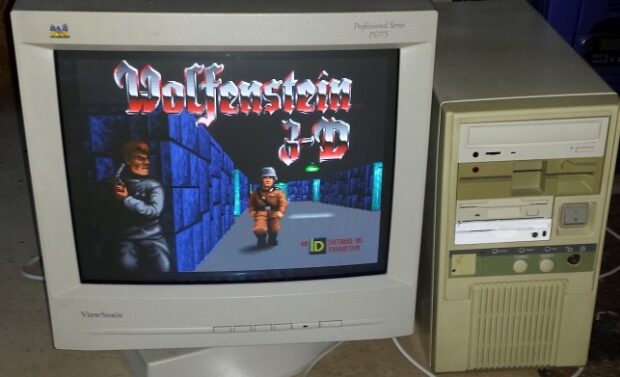
The Computer: My first computer was a 486 DX-2/80 with a floppy drive and 100 megabyte hard drive. Any phone made within the past several years puts this to shame. We now carry a pocket-size device which can send emails, browse the internet, and store 100x the data (at 1/10 the cost).
The Camera: I received a Pentax K-1000 35mm camera for Christmas in 1990. It was amazing. After taking a roll of pictures, I would drop the film off at Target and wait three days for my prints. There was no privacy. Today, we capture unlimited images with immediate private view at no cost. Modern cameras within mobile devices do not truly replicate the lens features of a manual camera, but the quality is much better than the first few rounds of 1-megapixel digital cameras. Digital cameras are basically free now.

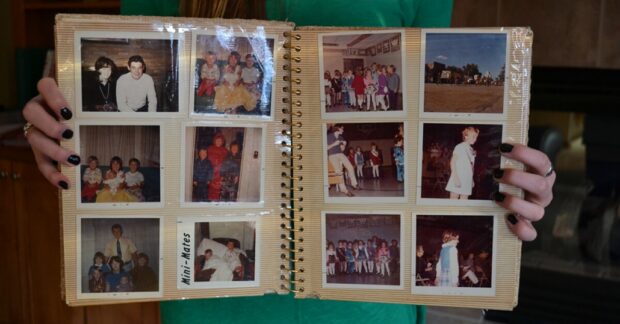
The Photo Album: We paid for film, then paid for development, then paid for physical storage. The cost to see 24 to 36 pictures was substantial. However, that made us appreciate the final images more. Today, we can store thousands of photos on our phone without much thought.
The Video Camera: Do you remember the cam-corder? My family could never afford one, but my friends had them. With a two-hour battery life and 6-hour VHS tape, the possibilities were endless. Today, our mobile devices possess a better quality video capture solution which fits in our pocket. We can store hundreds of hours of videos which we will never watch.

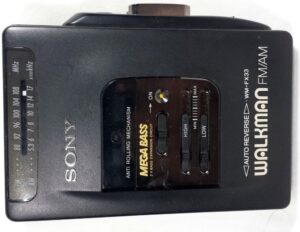
The Music Player: I had a Sony cassette Walkman in 5th grade. It had the MegaBass switch, which did not do much for my small foam headphones. However, it was HD quality to me. I carried it and a cassette caddy which stored up to six cassettes. I would eventually upgrade to a CD version and soft case which could carry 20 CDs. Today, I have hundreds of albums on my device ready to be played through high-quality headphones or the car stereo system.
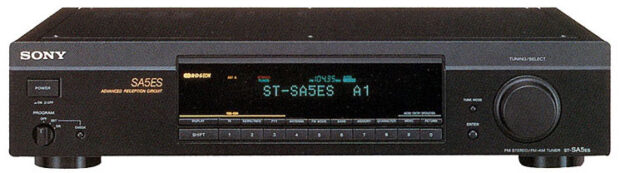
The Radio: My first rack stereo system had a digital radio tuner. This fascinated me. I began experimenting with antenna placement and reception of distant AM and FM stations. Today, many phones have an FM radio chip in them, but these are rarely used. Instead, we can stream practically any station throughout the world via the internet. Radio Garden and other apps allow us easy access to more broadcasts than we could ever consume. All stations are clearer than we could have ever heard them before.
The Weather Radio: This was THE Christmas gift for adults in the early 90's. You could tune into a weather report 24 hours a day, read by a computer generated voice. Even better, you could wake up to a deafening alert tone letting you know a mild storm was a few hours away from you. I believe many grandparents had one of these hanging on a wall, but very few left it enabled past a few days. Today, we have many choices of weather apps with detailed conditions and widgets which can update us hourly on our home screens.

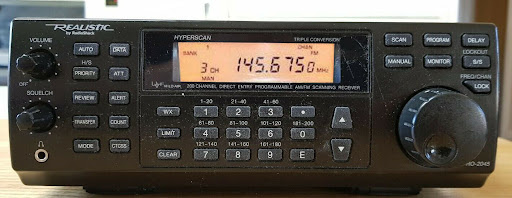
The Police Scanner: I was fascinated as a kid with the ability to "eavesdrop" on my local police at any time. My first scanner stored twenty frequencies and could scan through them all in 30 seconds. Today, we have apps which bring us police scanners from practically every city in the world. We don't need to purchase the equipment, antenna, or frequency books. We just need to point the app toward someone else's setup and reap the benefits.
The CB: When I was seven, I waited in the car while my aunt went into the bank. I saw her CB radio and picked up the microphone. I switched through the channels until "19" lit up with truckers talking about things I should not have heard. Without thinking, I pressed the mic and said "hello?", receiving an immediate unfriendly response. It scared the hell out of me. A few days later, I missed that rush and convinced my dad to let me borrow his portable CB radio. This began my interest in passively monitoring people during their public activities. Today, we have immediate 2-way communication through apps, and unlimited social network activity to creep on the world.

The Alarm Clock: One Christmas, I was upgraded from my manual alarm clock with buzzing tone to a radio clock which allowed me to wake up to any station I desired. This was a luxury to a latch-key 6th-grade student. Today, alarms are built into our devices with the ability to play any song, tone, podcast, or news report we want. They are battery powered and accurate. This eliminates the "my power went out" late-for-school excuse.

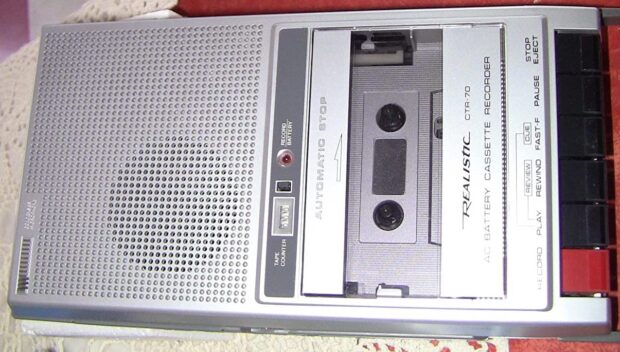
The Tape Recorder: My first tape recorder was a Christmas gift when I was in 2nd grade. I sang into it. I yelled into it. I complained about life into it. Then, I learned about making prank calls and recorded every one of them. I wish I had those tapes today. This was a specialty item. Today, every phone has the ability to record audio to digital file and store years of recordings, all without the need for a handle and 4 C-batteries.
The Phone Recorder: On a Friday night in 1985, I was exploring the shelves of my local radio shack. I discovered a suction-cup recording device which attached to a telephone and plugged into a tape recorder. It allowed you to capture both sides of a phone conversation for $1.99. This changed my prank calling adventures substantially. Today, we have apps which can intercept our calls and capture pristine recordings.

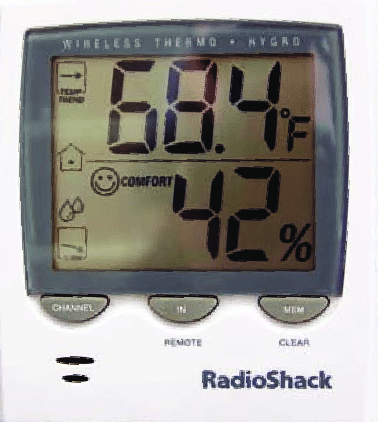
The Outdoor Thermometer: I bought one of these during Christmas of 1991 for my grandparents. It displayed the outdoor and indoor temperature and my grandfather checked it hourly. Today, we can load temps for anywhere in the world through a mobile app.
The Calculator: The solar-powered calculator was a big deal. No more batteries! I believe mine cost $9.99 and I played with it for hours. Today, calculator apps are included with our devices and overlooked.
The Contacts Organizer: My first digital organizer held 20 names and phone numbers. I was able to store all of my family's numbers, which I also knew by memory, which made it unnecessary. Today, our devices store unlimited full contact information and synchronize it effortlessly. I don't know anyone's number by memory today.
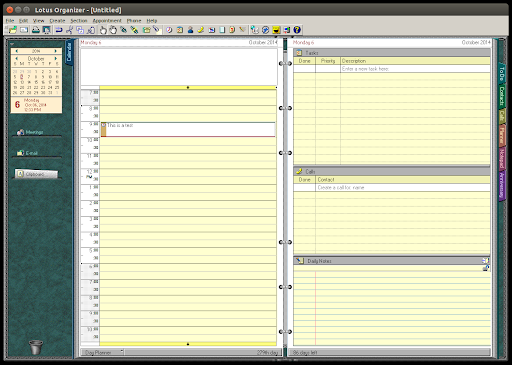
The Digital Calendar: I had a paper Day Runner when I was 12, but I soon upgraded to the Lotus Organizer software calendar on my computer. It did not synchronize to anything, and I had to launch the program whenever I wanted to review my (empty) calendar. Today, our devices synchronize our schedules, remind us about appointments, and alert us of important events. We once knew birthdays by memory, now we receive a notification.
The GPS Unit: My first Garmin was a free promotional unit with purchase of a laser printer. It had a 8MB SD card which could store basic roads of the entire country. I placed it in my car and then my jaw dropped. It magically knew my location at all times without any cellular or internet connection. Please remember this was in the early days of GPS. For almost a year, I let it guide me around a town with which I was very familiar just to soak up the technology. Today, GPS in embedded into all of our devices and maps are updated with real-time traffic conditions. It is practically impossible to get lost.

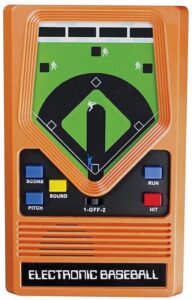
The Gaming Device: I had a passion for the handheld digital games of the 80's. I played baseball for hours looking at a random dot which I believed I was controlling. Today, we have unlimited HD games which mimic movie quality. We can even play them with our friends anywhere in the world. If we can put up with a few ads, they are all free. I think my devices which drained 9-volt batteries were $30 each. When I received a Gameboy with interchangeable cartridges, I assumed we had reached a peak in handheld gaming.
The DVD/VHS/Beta Player: Some of you may remember the Betamax war. When VHS won, we had to replace our tapes. When DVD came out, we had to switch to disc. When Blu-Ray came out, we had to upgrade our resolution. Today, our mobile devices can stream HD video which surpasses all of these mediums. A VHS movie was $19.99 to own, and looked awful. We now stream dozens of clear HD movies monthly at almost no cost.

The Universal Remote: I once purchased a Sony touch screen remote for $200. I could program the layout and my family thought I was nuts. Today, we can download apps which control our media devices from our phones. I use Yatse to control my Kodi server. It is free.

The Drum Machine: In 1987, I wanted to be a Beastie Boy. I borrowed a neighbor's drum machine and hit the buttons along with my dubbed cassette of Licensed To Ill. Today, free drum machine apps offer better sounds, timed loops, and realistic kits.

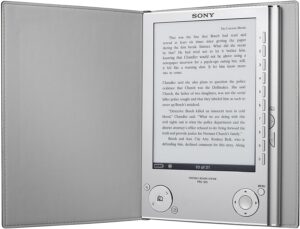
The Magazine/Newspaper/Book Reader: My first E-Reader was a heavy Sony device which stored about 20 books. It seemed unbelievable at the time. Then Kindles ruled the landscape. Today, our devices browse websites, download news feeds, ingest RSS, and store countless books for consumption.
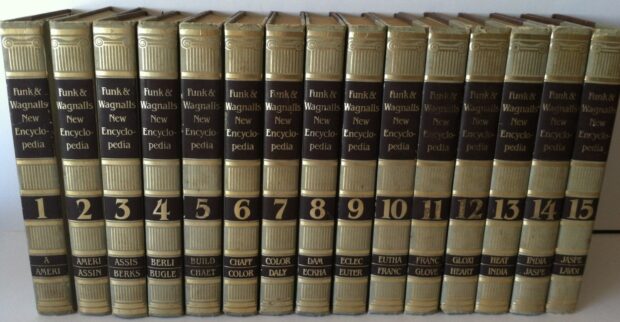
The Encyclopedia/Dictionary: In 1987 I received a set of encyclopedias for Christmas. It was not the most exciting gift, but useful for the next several years. Today, these are fairly extinct. We can fit the entire Wikipedia basic archive on our devices in the event we do not want to use our data access to look something up.
None of the features of a modern mobile device will ever replace the feel of tactile buttons and analog knobs for me. Today, I am grateful that technology has made all of this stuff freely enjoyable by anyone. However, I miss the effort which was required in order to enjoy my toys of the past. I miss reading instruction manuals before plugging in a device. I crave the hiss of a cassette tape or feel of a mechanical keyboard. As I finish this, I am looking at my Pixel 4a running GrapheneOS. The $300 device has replaced all of the gadgets I have presented here, with even better quality. We are so spoiled.